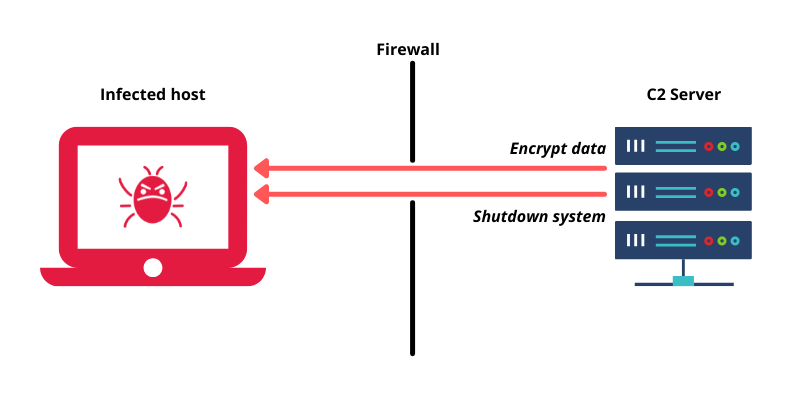
How a C2 Server is Leveraged in a Botnet Command and Control Attack | by Fikayo Adepoju | DNSFilter Blog | Medium
Deploying MBAM 2.5 in a stand-alone configuration - Microsoft Desktop Optimization Pack | Microsoft Learn

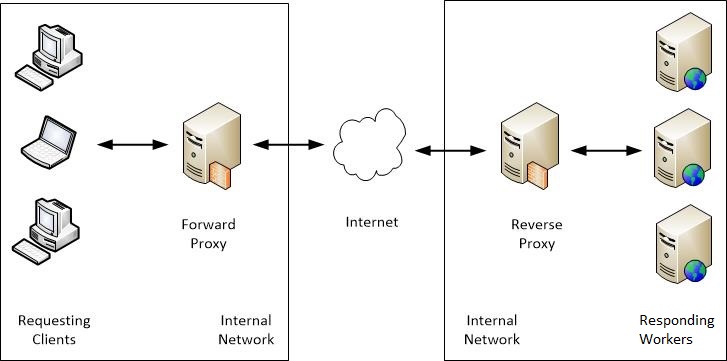
Proxying Atlassian server applications with Microsoft Internet Information Services (IIS) | Atlassian Support | Atlassian Documentation